
Support Team
Feedback:
support@nextpcb.comTo begin with remote access, ensure your Pi is running the most recent Raspberry Pi OS variant and is connected to a stable network. By 2026, the Compute Module 5 (CM5), based on the robust Raspberry Pi 5 architecture, has become the core standard component for industrial gateways, commercial displays, and robot main controllers. Because these advanced devices are often deployed in headless environments, setting up reliable remote access is more critical than ever.
Before exposing your device to any network, it is highly recommended to implement baseline security precautions:
sudo apt update && sudo apt upgrade.You will also need to know your Pi's unique IP address or set up a dynamic DNS service if you are operating on a dynamic WAN IP. Port forwarding may also be necessary if you are connecting remotely through a router or firewall.
Now that your Pi is secured and ready to be accessed, let's explore some of the most popular remote desktop protocols.
One of the most straightforward and widely supported options is VNC (Virtual Network Computing). To enable it:
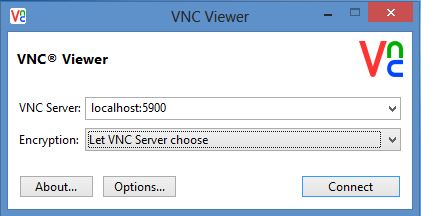
Figure 1: Enabling the VNC Server through the Raspberry Pi configuration tool.
sudo apt install tigervnc-standalone-serversudo raspi-config, then navigate to Interfacing Options > VNC.VNC transmits the full graphical user interface (GUI) over the network, though it may experience lag over high-latency connections. Alternatives like TightVNC might perform better in bandwidth-constrained scenarios. For enhanced security, always consider routing your VNC traffic through an SSH tunnel.
For Windows users, Microsoft's Remote Desktop Protocol (RDP) provides seamless, native integration:
sudo apt install xrdpraspi-config utility as demonstrated earlier.mstsc /v:IP_OR_HOSTNAMERDP utilizes excellent compression algorithms and offers comprehensive control over the remote Pi desktop. However, you might encounter occasional stability issues when operating over high-latency external networks.
While not a traditional full remote desktop solution, SSH with X11 forwarding allows you to remotely access individual graphical applications:
sudo apt install openssh-serverssh -X username@ip_addressX11 forwarding isolates single applications rather than streaming the entire desktop environment. This provides a lightweight, secure, and cross-platform alternative. Windows users can leverage this feature by running an X server software like Xming.
For a full-fledged, high-performance remote experience across multiple operating systems, NoMachine NX is an exceptional choice. It typically provides the fastest rendering performance among the available options:
sudo apt install nx-serversudo systemctl start nx-os-serverNX leverages highly optimized proprietary protocols. While commercial versions are paid, the free version is an invaluable asset for mission-critical remote access needs or when operating under poor network conditions where speed and fluidity are paramount.

Choose the protocol that best matches your specific workflow and network conditions. With the right setup, your Pi is securely controllable from anywhere on the globe.
When routing a remote session over the public internet, latency can significantly degrade the user experience. Consider these optimization tips:
With precise configuration, even moderate internet connections can facilitate highly productive remote access. Benchmark different protocols to discover which performs best in your specific network topology.
While remote capabilities open up unprecedented use cases, it is absolutely crucial to adhere to strict cybersecurity best practices:
Maintaining diligent authentication protocols and implementing a defense-in-depth strategy ensures you maximize convenience without compromising the safety of your hardware and local network.
To contextualize the power of remote desktop access, here are several practical project use cases:
By thoughtfully integrating remote access protocols, single-board computers exponentially expand their utility beyond direct physical interaction. Their localized computing power can now exert influence and gather data from afar.
A remotely accessible Raspberry Pi unlocks endless possibilities to interact with electronics projects, monitor network systems, and manage processing resources from any location with an internet connection. Whether you leverage VNC, RDP, SSH X11 forwarding, or specialized enterprise solutions like NoMachine, this guide has covered the most reliable methodologies for taking control of the Pi GUI desktop. When implemented securely and optimized for network latency, remote desktop technologies transform single-board computers into infinitely flexible platforms. The full potential of your device is now at your fingertips, regardless of your physical location.
This advanced setup involves configuring virtual console (VC) seats and managing XDMCP authentication, allowing multiple users to simultaneously log into their own isolated desktop environments using VNC or RDP, often managed via separate .Xauthority files.
By 2026, the Compute Module 5 (CM5), based on the Raspberry Pi 5 architecture, has become the core standard component for industrial gateways, commercial displays, and robot main controllers. Configuration for these systems abandons full desktop protocols in favor of headless SSH setups. Ensuring the SSH daemon auto-starts on boot and relies strictly on cryptographic key pairs is mandatory for these deployments.
Step-by-step methodologies for configuring Static and Dynamic NAT within your router's administration panel. This translates external internet requests on a specific port directly to the local IP address of your Raspberry Pi, bridging the local network with the public web.
Installation guides for DDNS clients. Since residential ISPs frequently rotate public IP addresses, a DDNS client periodically updates a registry, allowing you to consistently connect via a URL (e.g., my-pi.ddns.net) rather than tracking a moving IP target.
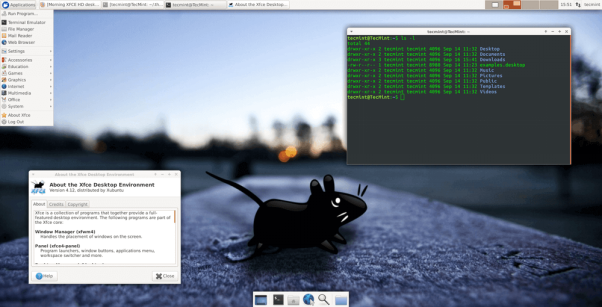
Optimization techniques for running heavy workloads remotely. This includes adjusting X11 configurations and utilizing lightweight desktop environments like LXDE or XFCE when manipulating demanding software like MATLAB or Eclipse IDE.
Creating bash scripts to automate repetitive remote tasks. Tools like expect or SSH command appending allow users to trigger application launches, run diagnostic commands, or reboot the device automatically based on Cron schedules.
Protocols for connecting directly to the Pi without an active internet connection. This includes configuring a direct crossover Ethernet link, setting up the Pi as a standalone WiFi access point, or utilizing static IP mapping on an offline switch.
Free Components Worldwide Shipping
Multiple Monitor Support: Advanced instructions for spanning a virtual remote session across dual local monitors, or conversely, transmitting the output of a multi-monitor Pi setup to a remote client.
3D Acceleration: Experimental configurations for enabling OpenGL and CUDA hardware acceleration within the remote session, vital for rendering CAD models, GIS mapping, and hardware-accelerated UI elements. Keep an eye out for potential driver bottlenecks.
Remote Printing: Setting up the Common UNIX Printing System (CUPS) to bridge the gap between local and remote networks, allowing a document generated on the Pi to print on your local desk printer.
Shared Folders: Utilizing Samba (SMB), NFS, or SSHFS to mount remote directories as local drives. This creates a frictionless workflow for dragging and dropping files between your main PC and the Raspberry Pi.
Remote Camera/IoT Access: Utilizing the remote desktop environment as a centralized command center to view live security feeds, monitor environmental sensor readouts, and actuate IoT relays connected directly to the Pi's GPIO pins.
KVM Switches: Integrating hardware-level KVM-over-IP devices (like PiKVM) to manage the boot sequence and BIOS/UEFI settings of multiple machines entirely out-of-band.
Wake on LAN (WoL): Configuring the Pi's network interface and BIOS (if applicable via specific hats) to power on the board from a suspended state upon receiving a "magic packet" over the network.
Collaboration Tools: Utilizing the Pi as an always-on collaboration server, hosting lightweight whiteboarding applications or local chat servers for encrypted team communication.
Accessibility: Customizing the remote session UI with screen magnifiers, adjusted color profiles, and screen-reader compatibility to ensure technology remains accessible for users with motor or visual impairments.
Q: What internet connection speed do I need for a smooth remote desktop experience?
A: Basic protocols like VNC and SSH X11 forwarding can operate effectively on modest bandwidths around 1-2 Mbps. Heavier protocols like RDP and NX require at least 3-5 Mbps to function properly. For a truly interactive, lag-free experience (especially when viewing media), a stable 5-10 Mbps connection is highly recommended. Lower latency (ping) is often more critical than raw bandwidth.
Q: Is remote access secure? Can hackers infiltrate my Pi?
A: Yes, if configured poorly, exposed ports invite brute-force attacks. However, strict adherence to security protocols—such as disabling password logins in favor of SSH keys, configuring UFW (Uncomplicated Firewall), using VPN tunnels (like Tailscale or WireGuard), and keeping software patched—makes the system highly secure. Never expose default remote ports directly to the open internet without an access control layer.
Q: How do I access my Pi externally if I cannot configure port forwarding on my router?
A: If you are behind Carrier-Grade NAT (CGNAT) or lack router access, leverage overlay networks and VPN services like Tailscale, ZeroTier, or Ngrok. These tools broker secure connections through external servers, bypassing the need for manual port forwarding.
Q: Can I use remote desktop software from my smartphone or tablet?
A: Absolutely. Major protocols like VNC, RDP, and NoMachine all offer dedicated applications for iOS and Android. TeamViewer is also exceptionally cross-platform. Be aware that navigating a desktop UI on a small touchscreen requires familiarizing yourself with specialized gesture controls.
Q: The remote display is extremely laggy and choppy, what troubleshooting steps should I take?
A: First, diagnose your local and remote network stability to rule out packet loss. On the Pi, disable compositing effects and animations to reduce rendering load. Within your client app, reduce the color depth (e.g., from 32-bit to 16-bit), lower the display resolution, and increase image compression. Ensure neither the Pi nor your client machine is maxing out its CPU.
Q: Can multiple users log into my Pi remotely at the exact same time?
A: Yes. By configuring the remote service daemon for concurrent access (such as utilizing the xfce4-multiple-users package or running x11vnc with multi-user flags), the system can spawn independent desktop sessions for each unique login.
Still, need help? Contact Us: support@nextpcb.com
Need a PCB or PCBA quote? Quote now